NERC CIP currently stands to be the oldest and most critical regulatory framework for protecting and securing our bulk electric systems as a whole as it relates to cybersecurity. On all levels, the consumer, through a corporation, NERC CIP sets the gold standard for operating and protecting the individuals who rely on its functionality. With so many mandated requirements, NERC CIP can be difficult to understand for those under-equipped, but knowing where to look and how to report on your organization's assets, policies, and personnel, can make the process digestible and replicable for your future compliance efforts. One of the things that makes NERC CIP unique is that it is centered around a risk-based model. To satisfy the controls within NERC CIP, your organization will have to account for everything it does, as it relates to operating in the BES, NERC outlines many resources available to meet these needs on their website.
What is NERC Compliance?
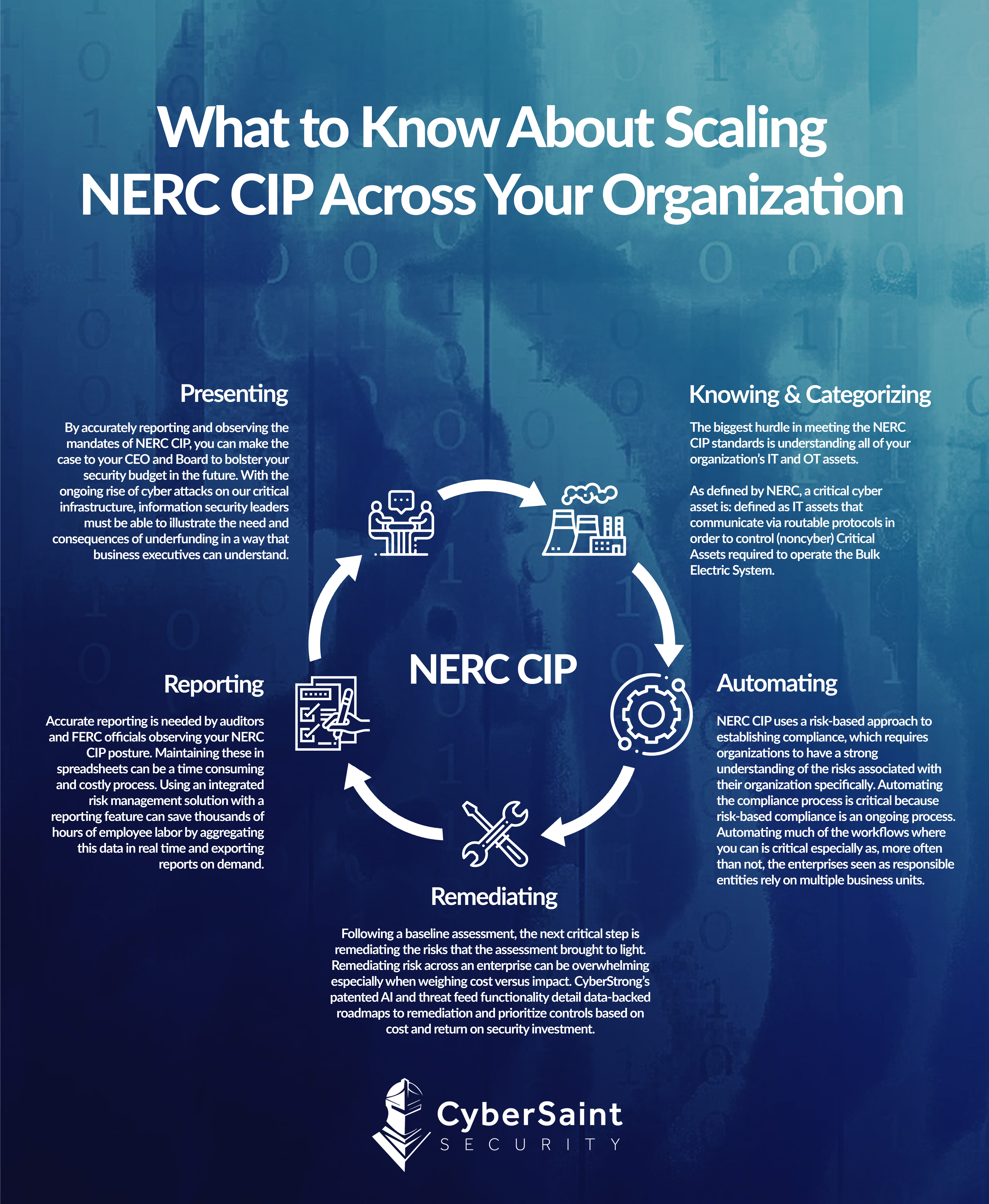
The standards of NERC CIP at the time of writing consist of 17 controls and 91 sub-requirements. Of these controls, only 11 are actively enforced, 5 are subject to future enforcement, and one is being transitioned to an inactive state. With this, we’ve developed a method to optimize your NERC CIP compliance efforts to speed up your risk initiatives and communicate them so your entire company can stay on the same page.
CyberStrong's cyber risk management platform empowers security teams to conduct real-time cyber risk assessments to assess the organization's security posture as controls change. Leverage a unique approach to continuous control monitoring using Continuous Control Automation (CCA) to manage and track your compliance with gold-standard frameworks like NERC CIP, NIST CSF, HIPPA, and ISO 27001.
Schedule a demo to learn more about the CyberStrong approach to cyber risk management.





.png)
.png)
.png)
%201.png)
.png)




